The measuring and statistical examination of an individual’s distinctive physical and behavioral traits is known as biometrics. The technology is mostly used for access control, identification, and for locating people who are being watched. The fundamental tenet of biometric authentication is that each individual may be precisely identified based on inherent physical or behavioral characteristics. The Greek words bio, which means life, and metric, which means to measure, are combined to form the phrase “biometrics.”
How Does Biometric Technology Operate?
Consumer gadgets, point-of-sale applications, and corporate and public security systems are all increasingly using biometric verification for authentication. Because there are no passwords to remember or security tokens to carry, biometric verification has been motivated by ease as much as security. Some biometric techniques, like gait analysis, can function without having any direct interaction with the person being validated. The following are components of biometric devices:
- a reader or scanning device to capture the authenticating biometric element;
- program to standardize the biometric data from scanning and to compare match points between observed and stored data; and
- a database for safely storing biometric information that can be compared.
Although modern biometric systems frequently rely on acquiring biometric data locally and then cryptographically hashing it so that authentication or identification may be carried out without direct access to the biometric data itself, biometric data may be stored in a centralized database.
Types of Biometric
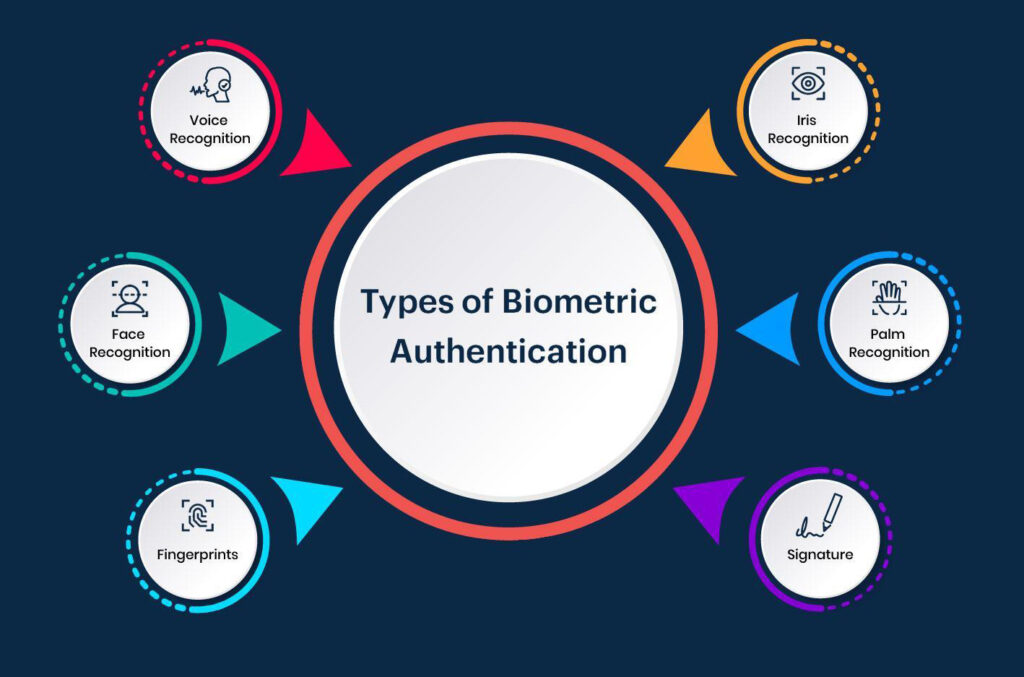
Physiological characteristics or behavioral characteristics are the two basic categories of biometric identification. The following are examples of physiological identifiers that relate to the make-up of the user being authenticated:
- facial recognition
- fingerprints
- finger geometry (the size and position of fingers)
- iris recognition
- vein recognition
- retina scanning
- voice recognition
- DNA (deoxyribonucleic acid) matching
- digital signatures
Individuals can be recognized by their distinctive behaviors, such as their typing patterns, mouse and finger motions, patterns of website and social media use, walking pace, and other gestures. Instead of doing a single one-off authentication check, several of these behavioral identifiers can offer continuous authentication. It has lower reliability ratings and is still a more recent method, but it has the potential to advance with other advancements in biometric technology. There are various applications for biometrics in addition to accessing information on a device like a smartphone using biometric data. For instance, biometric data may be stored on a smart card, in which case a recognition system would read a person’s biometric data and compare it to the biometric data stored on the smart card.
Benefits and Drawbacks of Biometrics
Regarding its use, security, and other connected functions, biometrics have a number of benefits and drawbacks. The following are some advantages of biometrics:
- unlike passwords, difficult to falsify or steal;
- simple and practical to utilize;
- generally constant over the duration of a user’s lifespan;
- nontransferable; and
- efficient because they require less storage space.
However, disadvantages include the following:
- It may be impossible to identify a person if the system is unable to collect all of the biometric information.
- A biometric authentication system might not function if a user is hurt. For instance, if a user burns their hand, a fingerprint scanner might not be able to identify them.
Biometrics are employed in many different industries in addition to the majority of cellphones now in use. For instance, the following industries and organizations apply biometrics:
Law enforcement:- It is utilized in criminal identification systems like palm or finger print authentication systems.
National Security:- It is utilized in Immigration Enforcement branches for a variety of detection, validation, and credentialing procedures, such as with facial recognition technology and electronic passports that save fingerprint information.
Healthcare:- It is utilized in programs and systems like national identity cards for identification and health insurance schemes that make use of fingerprints for identification.
Airport security:- This industry occasionally makes use of biometrics like iris recognition.
Privacy and Security Concerns with Biometrics
The uniqueness of the component under consideration affects the use of biometric IDs. For instance, it is generally accepted that each person’s fingerprints are extremely distinctive. The first widely utilized mass-market implementation of a biometric authentication element was fingerprint recognition. Other biometric components include voice, vein, eye, and retina scans. They haven’t been extensively embraced, though, in part because there is less trust in the IDs’ uniqueness or because the elements are simpler to forge and exploit for nefarious purposes, such identity theft. Acceptance of the biometric factor may also depend on the biometric factor’s stability. Unlike facial appearance, which can alter significantly with age, disease, and other causes, fingerprints do not change over the course of a lifetime. The fact that physical characteristics, such as fingerprints and retinal blood vessel patterns, are typically static and cannot be changed presents the biggest privacy concern with the use of biometrics. This is different from nonbiometric factors like tokens and passwords (which are something a person has and knows), which can be changed if they are compromised or breached. Biometrics will continue to be a more popular method of user authentication as high-quality cameras, microphones, and fingerprint readers are increasingly common in today’s mobile devices, especially since Fast ID Online has specified new standards for biometric authentication that support two-factor authentication with biometric factors. Even while biometric readers are getting better, they can still give erroneous results when an authorized user is recognized and validated, as well as false results when an unauthorized user is.
Biometrics: Are They Safe?
The usage of biometrics is made possible by high-quality cameras and other sensors, but they can also make an assault easier. Because people do not cover their faces, ears, hands, voices, or gaits, it is easy to launch attacks by secretly collecting biometric information about them. In 2002, Japanese researchers demonstrated how an attacker could lift a latent fingerprint off a glossy surface using a gelatin-based candy. This assault, known as the “gummy bear hack,” was the first to target fingerprint biometric identification. Given that jelly has a capacitance close to that of a human finger, the transfer of jelly might trick capacitance-based fingerprint scanners.

